Howto:How to configure NAT in V6
Network address translation is necessary to provide internal network stations with access to the stations in public internet and vice versa.
Network address translation is to be implemented at the border element (router) where the internal network (private IP addresses) meets the public internet (public IP addresses).
Applies To
This information applies to
- all innovaphone Gateways
build V6 and later
More Information
Type of address translation
There are several forms of address translation.
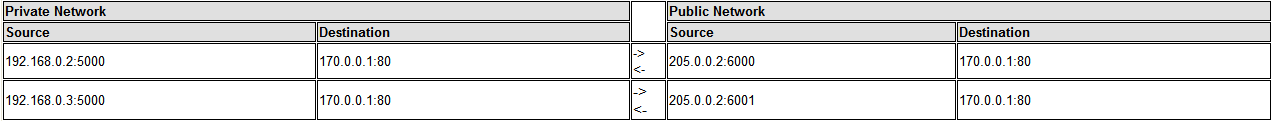
We do dynamic translation of multiple unregistered internal addresses to one single public address by changing the source port. Also known as „masquerading“ or „port address translation“.
Further you can configure static forwarding's of dedicated ports on the public address to the same port on an internal address.
NATed protocols
We do NAT for TCP, UDP, ICMP (only ECHO and TIMEX) and GRE (used for VPN).
Many application protocols (like HTTP) will work by simple NAT (forwarding) of transport layer protocol TCP.
For some application protocols (like H.323 or FTP) it’s not done by simply forwarding messages because the messages are used to exchange IP addresses between the communication endpoints.
The external station would get an internal IP address of the private network and would fail to talk to that address.
UDP
For UDP-NAT
DNS
We do a special handling for domain name resolution protocol.
DNS requests will not be forwarded to their actual destination address.
They rather will be forwarded to the DNS server address statically configured or dynamically assigned to the natting router.
H.323
To be able to use H.323 protocol between private and public network the connecting router must manipulate messages and forward the RTP media stream.
System Requirements − an innovaphone gateway used as internet router
− firmware version 6 or later
Configuration
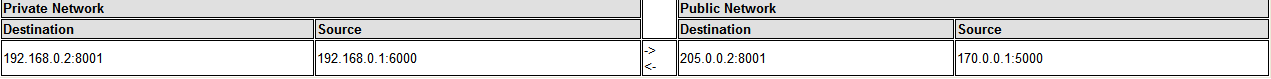
NAT can be generally enabled through the web based configuration interface.
Go to IP/NAT.
Enabling NAT
To enable network address translation just give a check mark to Enable NAT. This enables NAT functionality in general. Beside this overall checkmark you have to decide which of the local IP interfaces are to be included in or excluded from NAT. This per-interface configuration is to be done on the interface specific config pages.
You can also specify forwards to internal IP addresses. This allows someone in the public network to access services running on an station in the private network.
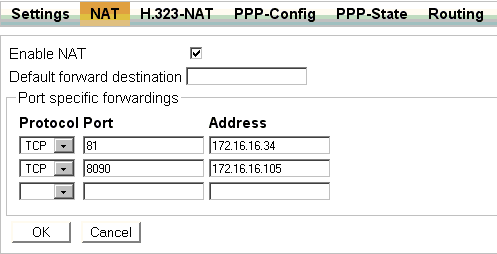
H.323-NAT
H.323-NAT is implemented as an add-on to the general NAT. You must configure NAT before you use H.323-NAT.
To allow internal H.323 devices (TEL/GW/GK) to open connections to external H.323 devices you must Enable H.323-NAT.
Further you can allow external H.323 devices to open connections to internal H.323 devices by defining static NAT destination for H.323.
If you want to allow external home offices to register at your private innovaphone PBX you must enter that internal address as H.225/RAS destination.
If you external ENUM users to connect to your private innovaphone PBX you must enter that internal address as H.225/Signalling destination.
To keep unauthorized H.323 traffic from entering the private network you can activate Require authentication.
The Status section provides information about currently active registrations and calls.
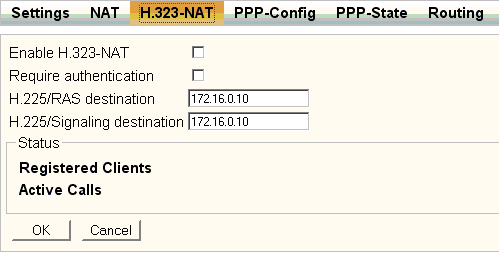
Excluding interfaces
As mentioned earlier the NAT functionality can be controlled in detail on a per interface basis.
By default all ETH interfaces are excluded from network address translation whereas PPP interfaces are included by default.
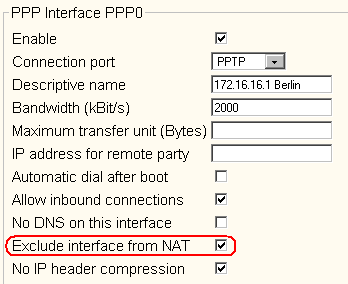
You can exclude selected PPP interfaces from network address translation by giving a check mark to Exclude interface from NAT.
You may exclude an interface from NAT to avoid address translation between different private networks.
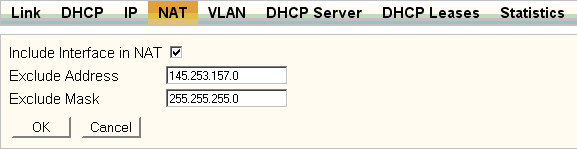
You can include an ETH interface in network address translation by giving a check mark to Include Interface in NAT.
You also can specify an address range that remains excluded from NAT on that interface.
This may be interesting to keep traffic between the private network and the DMZ from being natted.
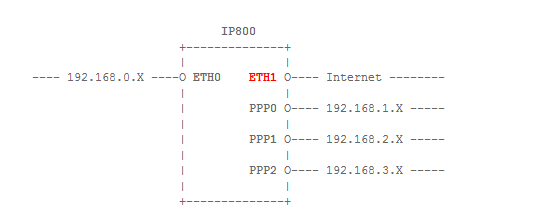
In the following example you only need address translation on the interface ETH1 (connected to the public network).
Traffic between all the private networks will find its destination anyway (as long as the IP800 knows the network address of each private network).
In this sample scenario you should enable NAT to have access to the public network from stations in all private networks but you should exclude PPP0 to PPP2 from NAT to keep the IP800 from wasting CPU time.