Howto13r1:Firewall Settings: Difference between revisions
| (10 intermediate revisions by 3 users not shown) | |||
| Line 1: | Line 1: | ||
<!-- Keywords: firewall settings, ports, workload, turn config, policies, firewall rules, firewall --> | <!-- Keywords: firewall settings, ports, workload, turn config, policies, firewall rules, firewall, tapete --> | ||
==Applies To== | ==Applies To== | ||
This information applies to | This information applies to | ||
| Line 9: | Line 9: | ||
Here we would like to give an overview of the necessary ports and protocols for Reverse Proxy, TURN and SBC in the DMZ. | Here we would like to give an overview of the necessary ports and protocols for Reverse Proxy, TURN and SBC in the DMZ. | ||
===Configuration=== | ===Firewall Configuration=== | ||
*Before you can setup your Firewall you have to read the book [[Course13:IT_Connect_-_10.0_Reverse_Proxy|Reverse Proxy]] in the [[Special:Prefixindex/Course13:|V13 IT Connect Training]]. | *Before you can setup your Firewall you have to read the book [[Course13:IT_Connect_-_10.0_Reverse_Proxy|Reverse Proxy]] in the [[Special:Prefixindex/Course13:|V13 IT Connect Training]]. | ||
| Line 18: | Line 17: | ||
! style="background-color: #EAECF0;text-align:center"|WAN ⇒ DMZ !! style="background-color: #EAECF0;text-align:center"|DMZ ⇒ inside (Endpoints) !! style="background-color: #EAECF0;text-align:center"|DMZ ⇒ inside (PBX) !! style="background-color: #EAECF0;text-align:center"|DMZ ⇒ inside (AP) !! style="background-color: #EAECF0;text-align:center"|inside ⇒ DMZ !! style="background-color: #EAECF0;text-align:center"|DMZ ⇒ WAN | ! style="background-color: #EAECF0;text-align:center"|WAN ⇒ DMZ !! style="background-color: #EAECF0;text-align:center"|DMZ ⇒ inside (Endpoints) !! style="background-color: #EAECF0;text-align:center"|DMZ ⇒ inside (PBX) !! style="background-color: #EAECF0;text-align:center"|DMZ ⇒ inside (AP) !! style="background-color: #EAECF0;text-align:center"|inside ⇒ DMZ !! style="background-color: #EAECF0;text-align:center"|DMZ ⇒ WAN | ||
|- | |- | ||
| STUN/TURN (udp/tcp/3478) || / || / || / || STUN/TURN (udp/tcp/3478)<br /> | | STUN/TURN (udp/tcp/3478) || / || / || / || STUN/TURN (udp/tcp/3478)<br /> || / | ||
''• <span style="font-size:11px;"> | |- | ||
|| / | | [[Reference13r3:IP4/General/STUN#TURN_Extern|TURN Extern]] (tcp/xxxx)<br>''• <span style="font-size:11px;">optionally TCP Port if you configure a fallback way</span>'' || / || / || / || [[Reference13r3:IP4/General/STUN#TURN_Extern|TURN Extern]] (tcp/xxxx)<br>''• <span style="font-size:11px;">optionally TCP Port if you configure a fallback way</span>''<br /> || / | ||
|- | |- | ||
| LDAPS (tcp/636)<br> | | LDAPS (tcp/636)<br> | ||
| Line 35: | Line 34: | ||
|| / | || / | ||
|- | |- | ||
| HTTPS (tcp/443)<br> | | HTTPS/WSS (tcp/443)<br> | ||
''• <span style="font-size:11px;">optionally HTTP (tcp/80) if you need plaintext</span>''<br> | ''• <span style="font-size:11px;">optionally HTTP/WS (tcp/80) if you need plaintext</span>''<br> | ||
''• <span style="font-size:11px;">needed if you want to offer myApps</span>''<br> | ''• <span style="font-size:11px;">needed if you want to offer myApps</span>''<br> | ||
''• <span style="font-size:11px;">please also allow wss/ws (websocket) connections</span>'' | ''• <span style="font-size:11px;">please also allow wss/ws (websocket) connections</span>'' | ||
|| / | || / | ||
|| HTTPS (tcp/443)<br> | || HTTPS/WSS (tcp/443)<br> | ||
''• <span style="font-size:11px;">optionally HTTP (tcp/80) if you need plaintext</span>''<br> | ''• <span style="font-size:11px;">optionally HTTP/WS (tcp/80) if you need plaintext</span>''<br> | ||
''• <span style="font-size:11px;">needed if you want to offer myApps</span>''<br> | ''• <span style="font-size:11px;">needed if you want to offer myApps</span>''<br> | ||
''• <span style="font-size:11px;">please also allow wss/ws (websocket) connections</span>'' | ''• <span style="font-size:11px;">please also allow wss/ws (websocket) connections</span>'' | ||
|| HTTPS (tcp/443)<br> | || HTTPS/WSS (tcp/443)<br> | ||
''• <span style="font-size:11px;">optionally HTTP (tcp/80) if you need plaintext</span>''<br> | ''• <span style="font-size:11px;">optionally HTTP/WS (tcp/80) if you need plaintext</span>''<br> | ||
''• <span style="font-size:11px;">needed if you want to offer myApps</span>''<br> | ''• <span style="font-size:11px;">needed if you want to offer myApps</span>''<br> | ||
''• <span style="font-size:11px;">please also allow wss/ws (websocket) connections</span>'' | ''• <span style="font-size:11px;">please also allow wss/ws (websocket) connections</span>'' | ||
| Line 76: | Line 75: | ||
|- | |- | ||
| / | | / | ||
|| RTP (udp/16384-32767, udp/50000-50299)<br> | || RTP (udp/16384-32767, [[Reference13r3:Concept_myApps_platform_services#RTP_service_for_audio.2C_video_and_data|udp/50000-50299]])<br> | ||
''• <span style="font-size:11px;">needed if you want to use RTP instead of TURN to inside. (eg. SIP Trunk with Media-Relay, TURN Server in DMZ)</span>'' | ''• <span style="font-size:11px;">needed if you want to use RTP instead of TURN to inside. (eg. SIP Trunk with Media-Relay, TURN Server in DMZ)</span>'' | ||
|| / || / | || / || / | ||
|| RTP (udp/16384-32767, udp/50000-50299)<br> | || RTP (udp/16384-32767, [[Reference13r3:Concept_myApps_platform_services#RTP_service_for_audio.2C_video_and_data|udp/50000-50299]])<br> | ||
''• <span style="font-size:11px;">needed if you want to use RTP instead of TURN to DMZ. (eg. SIP Trunk with Media-Relay, TURN Server in DMZ)</span>'' | ''• <span style="font-size:11px;">needed if you want to use RTP instead of TURN to DMZ. (eg. SIP Trunk with Media-Relay, TURN Server in DMZ)</span>'' | ||
|| RTP (udp/xxx)<br> | || RTP (udp/xxx)<br> | ||
| Line 86: | Line 85: | ||
|} | |} | ||
=== The complete Workload Picture | === Port Forwardings === | ||
If you have to use port forwardings often some of the needed ports are also needed by other systems (eg. Microsoft Exchange OWA access via tcp/443). If you run into this problem you have to forward the port to the reverse proxy and create rules (based on hostname) inside the reverse proxy to forward the traffic to the correct system. | |||
If you have multiple external ip addreses you can also use a separate ip address per system. See also [[Howto:V13_Installation_Scenarios#Possible_scenarios_if_port_443_is_already_in_use|Possible scenarios if port 443 is already in use]]. | |||
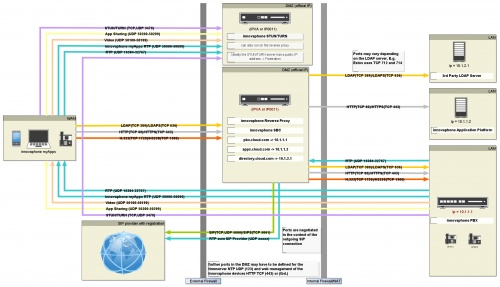
== The complete Workload Picture == | |||
[[Image:V13-workload.jpg|500px]] | [[Image:V13-workload.jpg|500px]] | ||
| Line 94: | Line 97: | ||
* [[Course13:IT_Connect_-_10.0_Reverse_Proxy]] | * [[Course13:IT_Connect_-_10.0_Reverse_Proxy]] | ||
* [[Course12:Advanced_-_Reverse_Proxy]] | * [[Course12:Advanced_-_Reverse_Proxy]] | ||
* [[Course13:IT_Advanced_2_-_06_Public_Access_to_PBX_Resources_(theory)_-_optional]] | |||
* [[Course13:IT_Advanced_2_-_07_Public_access_to_PBX_resources_(practice)]] | |||
[[Category:Howto|{{PAGENAME}}]] | [[Category:Howto|{{PAGENAME}}]] | ||
Latest revision as of 09:52, 19 October 2023
Applies To
This information applies to
V13 and up
Scenario: Reverse Proxy, TURN and SBC in a DMZ
Here we would like to give an overview of the necessary ports and protocols for Reverse Proxy, TURN and SBC in the DMZ.
Firewall Configuration
- Before you can setup your Firewall you have to read the book Reverse Proxy in the V13 IT Connect Training.
| WAN ⇒ DMZ | DMZ ⇒ inside (Endpoints) | DMZ ⇒ inside (PBX) | DMZ ⇒ inside (AP) | inside ⇒ DMZ | DMZ ⇒ WAN |
|---|---|---|---|---|---|
| STUN/TURN (udp/tcp/3478) | / | / | / | STUN/TURN (udp/tcp/3478) |
/ |
| TURN Extern (tcp/xxxx) • optionally TCP Port if you configure a fallback way |
/ | / | / | TURN Extern (tcp/xxxx) • optionally TCP Port if you configure a fallback way |
/ |
| LDAPS (tcp/636) • optionally LDAP (tcp/389) if you need plaintext |
/ | LDAPS (tcp/636) • optionally LDAP (tcp/389) if you need plaintext |
LDAPS (tcp/636) • optionally LDAP (tcp/389) if you need plaintext |
/ | / |
| HTTPS/WSS (tcp/443) • optionally HTTP/WS (tcp/80) if you need plaintext |
/ | HTTPS/WSS (tcp/443) • optionally HTTP/WS (tcp/80) if you need plaintext |
HTTPS/WSS (tcp/443) • optionally HTTP/WS (tcp/80) if you need plaintext |
HTTPS (tcp/<your custom port>) • Advanced UI admin access |
/ |
| H.323 (tcp/1300) • optionally H.323 (tcp/1720) if you need plaintext |
/ | H.323 (tcp/1300) • optionally H.323 (tcp/1720) if you need plaintext or username/password auths with invalid certificates |
/ | / | / |
| SIPS (tcp/5061) • optionally SIP (tcp/5060) if you need plaintext |
/ | SIPS (tcp/5061) • optionally SIP (tcp/5060) if you need plaintext |
/ | / | SIPS (tcp/5061) • optionally SIP (tcp/5060) if you need plaintext |
| / | RTP (udp/16384-32767, udp/50000-50299) • needed if you want to use RTP instead of TURN to inside. (eg. SIP Trunk with Media-Relay, TURN Server in DMZ) |
/ | / | RTP (udp/16384-32767, udp/50000-50299) • needed if you want to use RTP instead of TURN to DMZ. (eg. SIP Trunk with Media-Relay, TURN Server in DMZ) |
RTP (udp/xxx) • xxx are the negotiated ports in context of the outgoing sip/udp connection. The ports depend on your SIP Provider |
Port Forwardings
If you have to use port forwardings often some of the needed ports are also needed by other systems (eg. Microsoft Exchange OWA access via tcp/443). If you run into this problem you have to forward the port to the reverse proxy and create rules (based on hostname) inside the reverse proxy to forward the traffic to the correct system. If you have multiple external ip addreses you can also use a separate ip address per system. See also Possible scenarios if port 443 is already in use.