Reference7:Certificate management
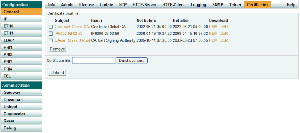
Trust list
This list contains the certificates to be accepted for TLS connections (e.g. HTTPS, SIPS). You can add either individual endpoint certificates or a CA certificate if you want to accept all certificates issued by that CA.
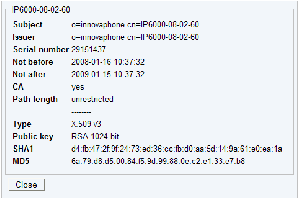
Certificate details
- Click the subject name to view the details.
Installing a certificate from a file
- Select a file.
- Press the "Upload" button.
- Take a look at the certificate details and check wheather the SHA1 and MD5 fingerprints match with the values published by the owner.
Note: PEM files can contain multiple certificates.
Installing a certificate that was rejected before
See section "Rejected certificates".
Removing single certificates from the trust list
- Select the items to remove using the checkboxes.
- Press the "Remove" button.
Open TLS connections that are using these certificates will not be closed.
Removing all certificates from the trust list
- Press the "Clear" button.
Open TLS connections that are using these certificates will not be closed.
Download
You can download an individual certificate from the trust list in PEM and DER format by clicking the corresponding link. Additionally you can download the complete list as a text file containing the PEM encoded certificates.
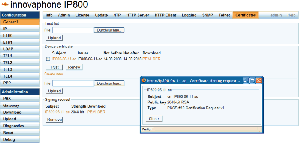
Rejected certificates
This list contains the certificate chains that were rejected before, while trying to establish a secure TLS connection. This happens for example if the certificate is expired or neither the certificate nor any of the issuing CAs is trusted. If one of that certificates should be trusted for future connections you can select and add it to the trust list, directly.
Certificate details
- Click the subject name to view the details.
Removing all certificates from the list
- Press the "Clear" button.
Adding rejected certificates to the trust list
- Check the certificate details and decide wheather it should be trusted or not.
- Select certificates using the checkboxes and press the "Trust" button.
Certificates can only be trusted if they are valid (i.e. not expired).
Fast trust list setup in small installations
- Set up your devices without taking care for the trust list
- Clear the list of rejected certificates
- Make a test run (Shouldn't work!)
- Trust the rejected certificates
- Make a test run again (Should work this time!)
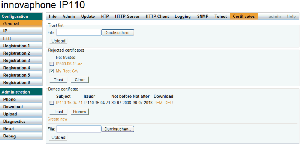
Device certificate
The device certificate can be used by remote TLS endpoints to authenticate the identity of the device. In general this is not a single certificate but a chain containing the device certificate and the certificates of the intermediate CAs up to the root CA. A TLS connection can only be established if the remote endpoint trusts at least one of that certificates.
An RSA key pair is associated with this certificate. The certificate that contains the public key is used to authenticate the box to its clients. They can use the public key to encrypt messages for the box and to validate its signatures. The private key is used for decryption and signing and remains on the box.
Certificate details
- Click the subject name to view the details.
Default certificate
If a device does not have a certificate (e.g. after upgrading from older firmware versions) a new key pair and a self-signed certificate are being created, automatically. It will contain the netbios name of the device (e.g. IP800-06-11-ac) and will be valid for 10 years.
- If the certificate is expired, press the "Renew" button to create a new one.
HTTPS and SIPS are deactivated while the default certificate is being created.
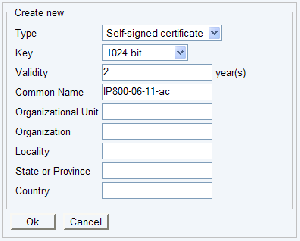
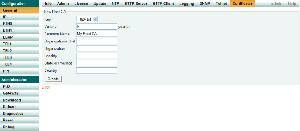
Creating a self-signed certificate
A self-signed certificate is not signed with the key of a separate CA but with the key of the owner itself. Therefore the issuer and subject name is the same. Such a certificate cannot be validated by parties that dont know the owner.
- Click the "Create new" link.
- Select "Self-signed certificate".
- Specify the number of years the certificate shall be valid.
- Choose the desired key strength or to reuse the old keypair (not recommended).
- Specify a distinguished name.
- Press the "OK" button.
- Wait until the new key pair and the certificate is ready. This may take a long time, depending on the selected key strength.
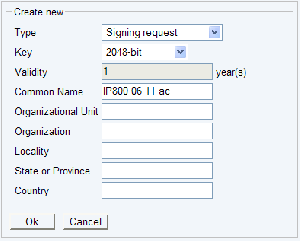
Creating a certificate signing request
A certificate signing request contains a public key and an identity. While the correponding private key is kept secret, the request is being sent to a CA. It will issue an appropriate certificate for the public key after it verified the identity.
- Click the "Create new" link.
- Select "Signing request".
- Choose the desired key strength or to reuse the old keypair (not recommended).
- Specify a distinguished name.
- Press the "OK" button.
- Wait until the new key pair and the request is ready. This may take a long time, depending on the selected key strength.
- Download the request by clicking the PEM and DER link, respectively.
- Send the request to your CA.
After you got your certificate from the CA, proceed with section "Uploading a certificate derived from a certificate signing request".
Uploading a certificate derived from a certificate signing request
- Select the certificate file.
- Click the "Upload" button.
This will only work, if there is a corresponding certificate signing request with the private key on the box.
Uploading a certificate chain together with the private key
Warning: It is mandatory to use HTTPS for this operation in order to keep the private key secret!
- Select a file.
- Press the "Upload" button.
Please use a PEM file containing the certificate chain from the device certificate up to the root CA certificate. Additionally the file must contain the corresponding private key.
Device certificate -----BEGIN CERTIFICATE----- MIICMTCCAZqgAwIBAgIBATANBgkqhkiG9w0BAQUFADAVMRMwEQYDVQQDDApNeSBS b290IENBMB4XDTA4MDgxNDA5MDkzM1oXDTExMDgxNDA5MDkzM1owGTEXMBUGA1UE 7HNL76EuQrMmshxYxq0Ay/mlkVc0v7Fp1NzkYn0I2UHpwFZ+zA== -----END CERTIFICATE----- Intermediate CA certificate -----BEGIN CERTIFICATE----- MIICDDCCAXWgAwIBAgIBADANBgkqhkiG9w0BAQUFADAVMRMwEQYDVQQDDApNeSBS 3FSCPvWfh5nk4e8wIAYDVR0OAQEABBYEFE5lzuLAhex3qtxUgj71n4eZ5OHvMA0G CSqGSIb3DQEBBQUAA4GBAAepePqAM59TSoZvSPM/XUn3WKbeOa++6842+4Vp9B1c NmI952d/j/+VsuUXDzPff92IsumPBcch87pksp2GkDrnBvd8WxRsm/n6JF2XS2Ey -----END CERTIFICATE----- Root CA certificate -----BEGIN CERTIFICATE----- MIICDDCCAXWgAwIBAgIBtpmdSuc+WKAS1UZHbtUFADAVEpG4C3G4CQYDVQQDDApe cmKMZ+WFAkEA5e4thgPIFPjLtVL2EK7WxMi2msigZ0HeoBfAJHu5K/H01BqUGdwK hh+ksaW+DStVNG21iuZSQuGwVv56oHj3fQJAdHx+06d7p3G4CA2fdfg24iopluMA oQN9N7Dfw4RyD+ypsMYz8at9RTEqG8Lc0hujGLgtvBpHUp6wxdUuRw4DJQJAGqn0 PYZSvZvcg7qLLoQYA9oC0xBRCahp2MboUVLHtoDok3BBnH4X+lXRE4jU8VIFH39Z -----END CERTIFICATE----- Device private key -----BEGIN RSA PRIVATE KEY----- MIICXAIBAAKBgQDecOKfxrVdHNZRl8RnpNItpmdSuc+WKAS1UZHbtdH5dUJ7OzG3 ZtW684dkm+mbLP00uY4Qiu25dNg0pKp7svihPU8AvKjoyIS52R2Mtt+/hTpjDfgj mGFyhMMmziCLaC+oKL4W88sivv7oOjUlBmGHc0JarKoN1q3Yxgcfg4Zk8QIDAQAB UcVghAbSXJ5G3A3v9POs8UthRMxPrnN2c7DadjZp7Qg= -----END RSA PRIVATE KEY-----
Downloading the device certificate
You can download a single certificate from the device certificate chain. For example this is needed if you want to configure your web browser to trust it.
- Click the "PEM" or "DER" link of the certificate you want to download.
Downloading the complete certificate chain and the private key
You can also download the complete certificate chain together with the private key in order to transfer it to another device.
Warning: It is strongly recommended not to do that without a good reason. It is mandatory to use HTTPS for this operation in order to keep the private key secret!
- Click the "Download chain and private key" link.
- Save the file on your PC.
The default certificate cannot be downloaded.
Deleting the certificate
Warning: This will discard the current device certificate chain and the private key, permanently!
- Press the "Clear" button.
The default certificate will be restored. If there is no default certificate, a new one will be created.
Replacing a device transparently
Warning: It is mandatory to use HTTPS for this operation in order to keep the private key secret!
If you want to replace device A by device B and you want B to have the same certificate as A
- Download the certificate chain and the private key from box A (See section "Downloading the complete certificate chain and the private key").
- Upload the file to box B (See section "Uploading a certificate chain together with the private key").
- Delete the certificate from device A (See section "Deleting the certificate").
Warning: It is mandatory to use HTTPS for this operation in order to keep the private key secret!
- Download the certificate chain and the private key from box A (See section "Downloading the complete certificate chain and the private key").
- Upload the file to box B (See section "Uploading a certificate chain together with the private key").
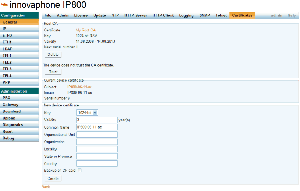
Root certification authority on Compact Flash card
This is the recommended approach to securely deloying PKI to innovaphone gateways.
- The private key of the CA is never being sent over the network or stored on a device.
- You only have to add a single certificate to the trust list of your devices.
Setting up the Root CA
- Insert an empty CF card into the card slot of a gateway.
- Click the "Root CA" link.
- Specify the desired bit strength, validity and distinguished name for the certificate and click the "Create" button.
- Wait until the private key and the certificate have been created.
- Check the certificate details.
- Remove the CF card and keep it at a safe place or continue with creating a device certificate.
Creating a device certificate
- Insert the CF card into the card slot of a gateway.
- Click the "Root CA" link.
- Most probably you want to add the root CA certificate to the trust list of the device. Click the "Trust" button.
- Specify the desired bit strength, validity and distinguished name for the certificate.
- Select "Backup on CF card", if you want to store the newly created private key and certificate on the CF card.
- Click the "Create" button.
- Wait until the private key and the certificate have been created.
- Check the certificate details.
- Remove the CF card and keep it at a safe place.
Supported features
File formats
- DER (Distinguished Encoding Rules, Extensions .crt .cer .der)
- PEM (Personal E-Mail, Extensions .pem .txt)
Certificate types
- X.509 versions 1-3
Certificate extensions
- basicConstraints
- keyUsage
- extKeyUsage
- subjectAltName
- subjectKeyIdentifier
- authorityKeyIdentifier
Note: Validation will fail, if an unsupported extension is marked as critical.
Signing algorithms
- sha1WithRSAEncryption
- md5WithRSAEncryption (only decoding)
Keys types
RSA keys
- 1024-bit (default)
- 2048-bit
- 4096-bit