Howto14r2:Step-by-Step Distribute a custom device certificate: Difference between revisions
| Line 75: | Line 75: | ||
== Known issues == | == Known issues == | ||
===High CPU load === | ===High CPU load === | ||
We only recommend to use a certificate that uses 2048 bit public key length. | We only recommend to use a certificate that uses 2048 bit public key length. | ||
===Certificate Key Format=== | |||
Certificate authorities may provide a certificate key in a format other than PKCS#1, such as PKCS#8. If you upload the certificate using the '' General/Certificates'' advanced UI, the firmware will convert it to the required PKCS#1 format. However, if you distribute the certificate key via variables, as shown here, you must distribute it in PKCS#1 format. To convert the key from one format to another, you can use a tool such as OpenSSL. Refer to the OpenSSL documentation to find the correct command. For example, converting a PKCS#8 to a PKCS#1 key can be done using the command <code>openssl rsa -in pkcs8.key -traditional -out pkcs1.key</code> | |||
== Related Articles == | == Related Articles == | ||
*[[Courseware:IT_Advanced_-_09_Custom_certificates]] | *[[Courseware:IT_Advanced_-_09_Custom_certificates]] | ||
*[[Reference11r1:Certificate_management]] | *[[Reference11r1:Certificate_management]] | ||
Latest revision as of 16:17, 28 April 2026
If you have difficulty understanding the written language, we recommend to use www.deepl.com for translation.
If installed, you can also use the translation function of your browser by right-clicking.
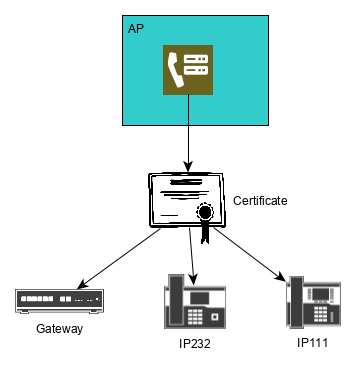
This article describes a method to roll out a custom certificate to innovaphone devices.
Purpose
Some customers run their own public key infrastructure (PKI) and want to use their own certificate (eg a wildcard certificate like *.company.com). This way you can distribute this certificate to all innovaphone devices.
Features
- A convenient way to distribute a custom device certificate
- Reboot is not necessary
Limitations
- The length of the public key should not exceed 2048 bits. This is to limit the CPU consumption on our devices, see Certificate management for details.
Requirements
- Devices App
- Innovaphone PBX
- Firmware should be at least v14r2sr4
- You need a complete certificate chain containing the private key. We recommend to use a PEM encoded Text file as explained here.
- Wireshark
Things to know before you begin
- The certificate device configuration in your Devices app only maintains your trust list. As a result it will not distribute the device certificate.
- The pre-installed certificate signed by the Inno-CA remains in the Flash when you upload a new certificate. If you delete the new certificate, the pre-installed certificate will reappear.
Configuration
Create Expert configuration
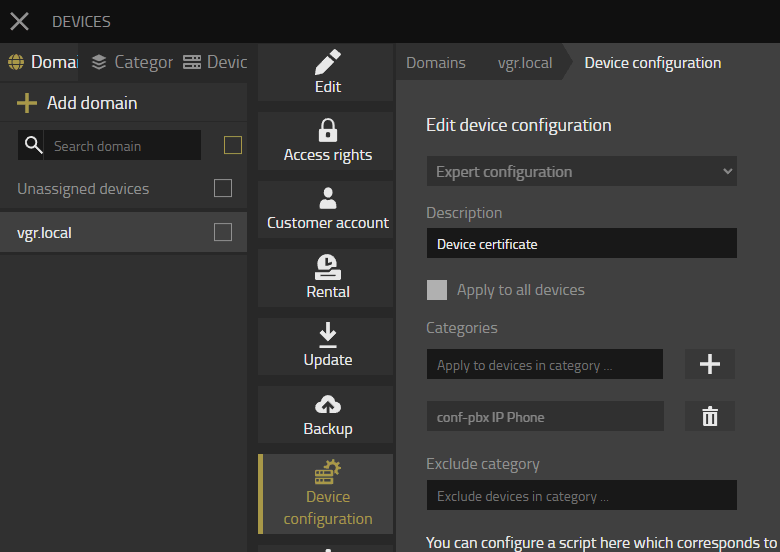
- Open your Devices App-><your Domain>->Device Configuration->Define device configuration->Expert
- Assign a Description e.g Device certificate
- Assign the provisioning category to this device configuration that should receive the new device certificate
Get VARS
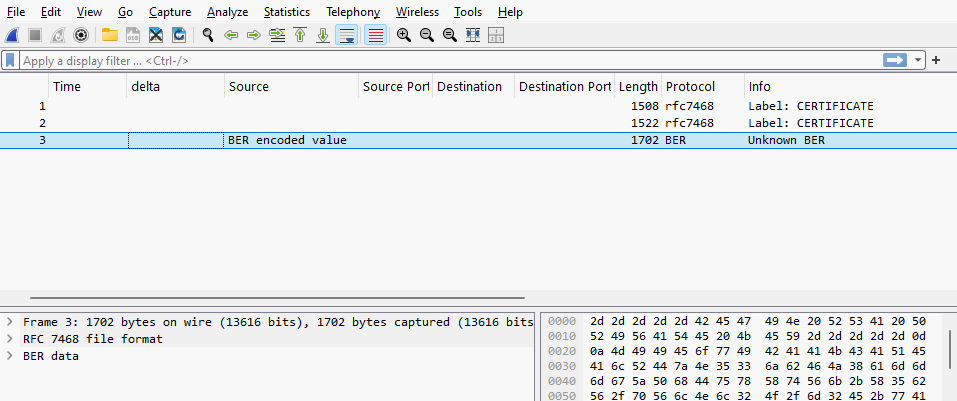
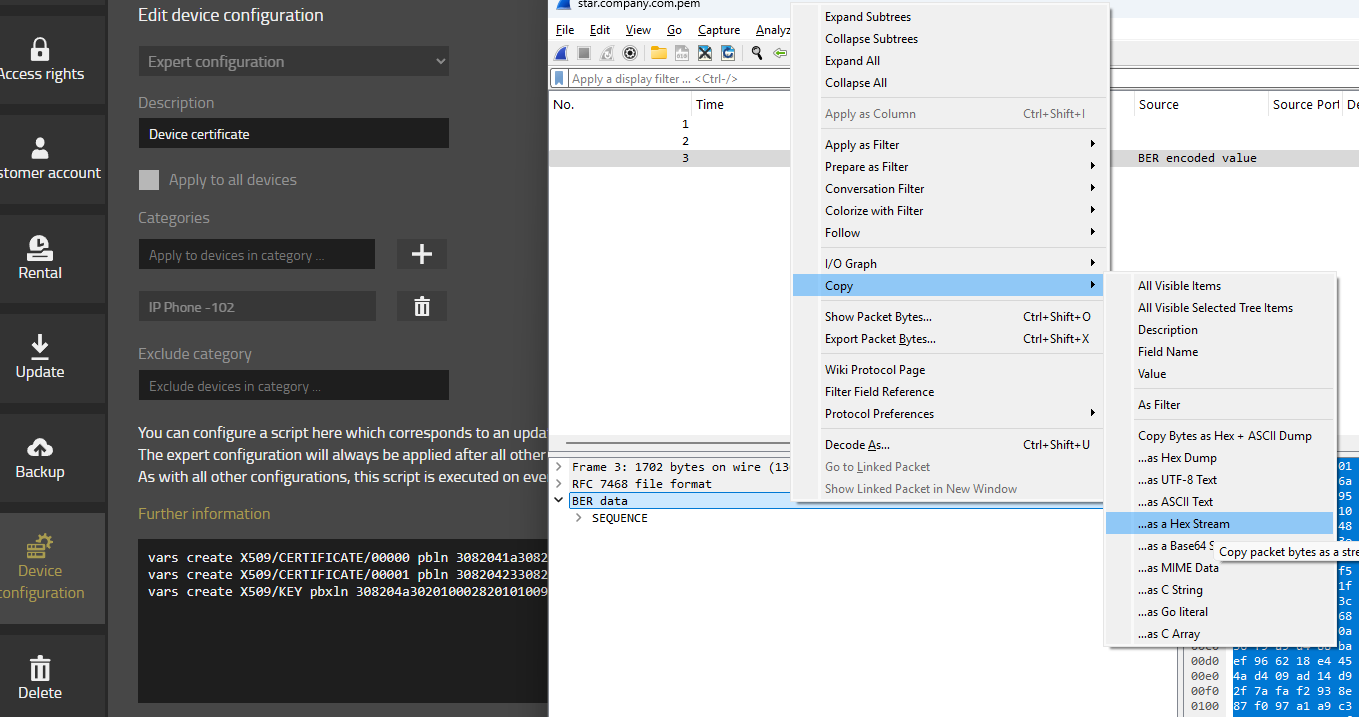
- Open your Wireshark
- Drag and drop the PEM file into your Wireshark
- Your Wireshark will only display a few packets
- Click on the first packet
- Do a right click on the section starting with Certificate
- Select Copy and then Copy as Hex stream
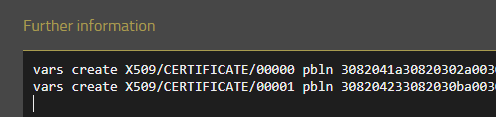
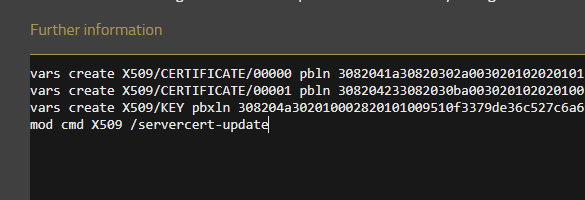
- Create a first line in your Expert configuration starting with vars create X509/CERTIFICATE/00000 pbln and paste the Hex stream from wireshark to the end of the line
- Then repeat the same procedure for each certificate in the certificate chain, but increase the index by 1. e.g. vars create X509/CERTIFICATE/00001
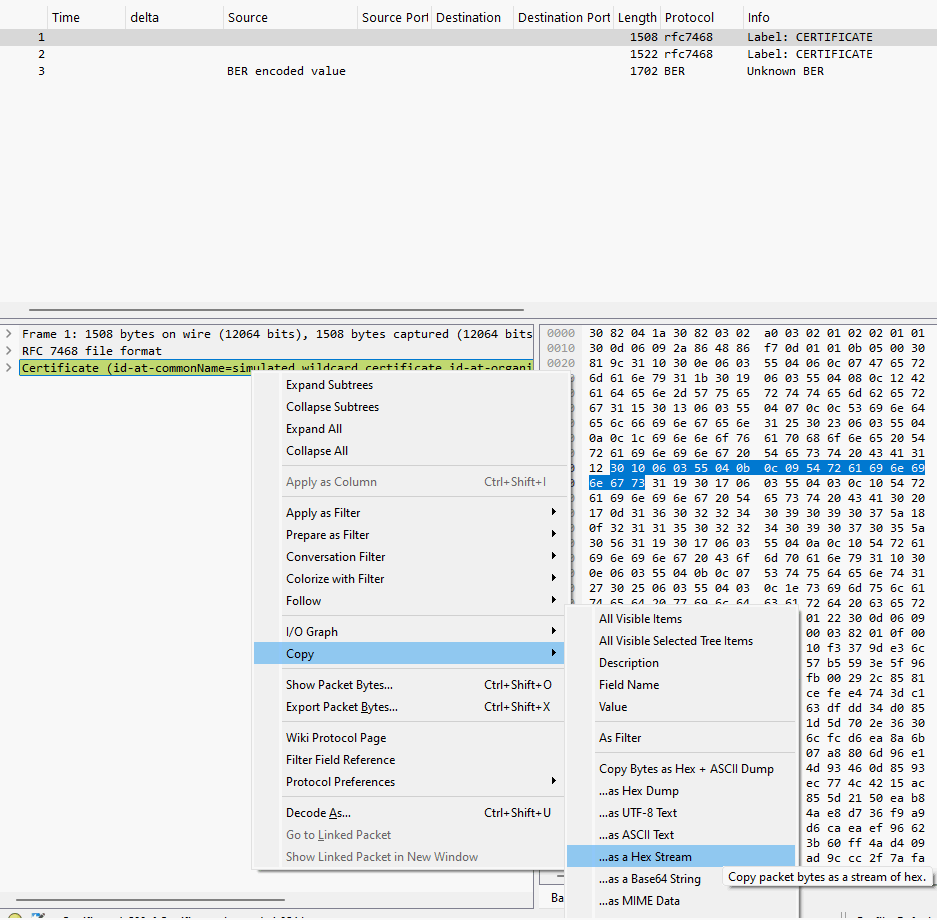
The private key has to be copied as well.
- Open the last packet in Wireshark and select the BER section. Copy the section as Hex stream as well.
- Create a line vars create X509/KEY pbxln and paste the Hex stream from the BER packet to the end of the line.
If no BER section is available, open the PRIVATE KEY packet instead.
Expand the PrivateKeyInfo structure and locate the entry privateKey.
Copy this section as a Hex stream as well, and use it in the same way as described above.
Finish Expert configuration
- The last line in our script is: mod cmd X509 /servercert-update
- In the end the expert configuration should look like this:
- As soon as you save the configuration, the device certificate will be pushed.
Verification
Look at the Advanced UI of the device. You should see a new Device certificate on General/Certificates
Known issues
High CPU load
We only recommend to use a certificate that uses 2048 bit public key length.
Certificate Key Format
Certificate authorities may provide a certificate key in a format other than PKCS#1, such as PKCS#8. If you upload the certificate using the General/Certificates advanced UI, the firmware will convert it to the required PKCS#1 format. However, if you distribute the certificate key via variables, as shown here, you must distribute it in PKCS#1 format. To convert the key from one format to another, you can use a tool such as OpenSSL. Refer to the OpenSSL documentation to find the correct command. For example, converting a PKCS#8 to a PKCS#1 key can be done using the command openssl rsa -in pkcs8.key -traditional -out pkcs1.key