Concept 802.1X
Info
802.1X, Port-Based Network Control, is an IEEE standard. The standard allows network devices to perform an authentication handshake within the 802.3 link layer (Ethernet). The authentication is encapsulated within EAP over LAN (EAPOL) frames. No other traffic, except EAPOL is allowed prior to a successful authentication. 802.1X must not be considered a bullet-proof security mechanism, since all traffic following the authentication phase is not authenticated.
The standard specifies the following parties participating in an 802.1X authentication:
- Supplicant: The party supplying credentials towards an authenticator on the other side of a point-to-point link. For example an IP phone fulfills a supplicant's role.
- innovaphones IP-phones are configured to support pass-through of EAPOL messages. That means a PC attached to the PC-port of a phone may also become a supplicant and may 802.1X-authenticate independently and separately.
- Authenticator: The party facilitating the authentication. A switch will usually be the authenticator and forward the authentication messages to an configured Authentication Server.
- Authentication Server: The party providing the authentication service to the authenticator. The 802.1X standard mentions a RADIUS server to be an authentication server.
It is the Authenticator/Authentication Server deciding whether EAP-MD5 or EAP-TLS is going to be applied.
- Sample Protocol Flow, EAP-MD5:
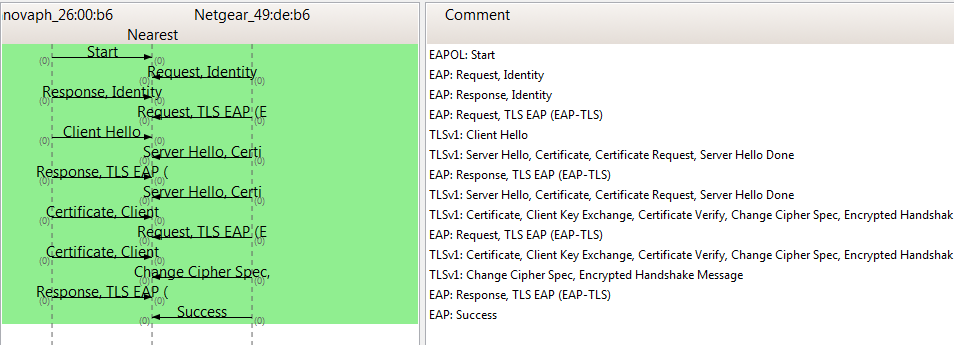
- Sample Protocol Flow, EAP-TLS:
Debugging
The software module is capable of generating internal trace messages and RPCAP PDUs. Tracing can be enabled by activating a checkmark on the /debug.xml page of the firmware's web UI. The checkmark is named ENET1X0 (for interface ETH0). The trace buffer can be fetched by a PC connected directly to the PC-port.
Known Limitations
Related Articles